 实验四IPSec综合实验.docx
实验四IPSec综合实验.docx
- 文档编号:3512956
- 上传时间:2022-11-23
- 格式:DOCX
- 页数:8
- 大小:36.06KB
实验四IPSec综合实验.docx
《实验四IPSec综合实验.docx》由会员分享,可在线阅读,更多相关《实验四IPSec综合实验.docx(8页珍藏版)》请在冰豆网上搜索。
实验四IPSec综合实验
实验四:
IPSec实验
实验需求:
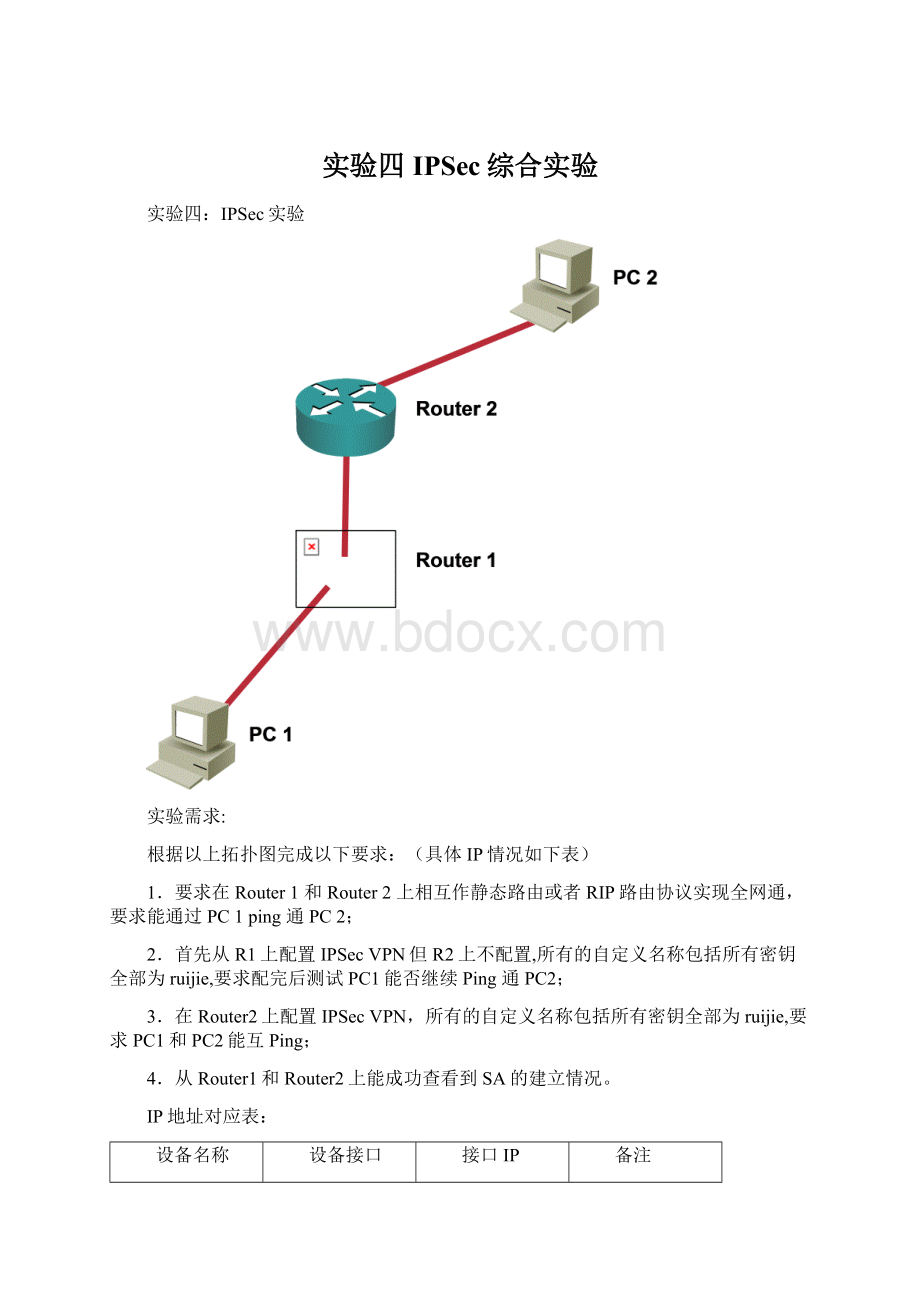
根据以上拓扑图完成以下要求:
(具体IP情况如下表)
1.要求在Router1和Router2上相互作静态路由或者RIP路由协议实现全网通,要求能通过PC1ping通PC2;
2.首先从R1上配置IPSecVPN但R2上不配置,所有的自定义名称包括所有密钥全部为ruijie,要求配完后测试PC1能否继续Ping通PC2;
3.在Router2上配置IPSecVPN,所有的自定义名称包括所有密钥全部为ruijie,要求PC1和PC2能互Ping;
4.从Router1和Router2上能成功查看到SA的建立情况。
IP地址对应表:
设备名称
设备接口
接口IP
备注
PC1
网卡
192.168.1.1/24
Router1
FastEthernet0/1
192.168.1.254/24
Router1
FastEthernet0/0
192.168.2.1/30
Router2
FastEthernet0/0
192.168.2.2/30
Router2
FastEthernet0/1
192.168.3.254/24
PC2
网卡
192.168.3.1/24
配置清单:
路由器IP配置清单
RSR20-01>en14
Password:
RSR20-01#conft
Enterconfigurationcommands,oneperline.EndwithCNTL/Z.
RSR20-01(config)#intfa0/1
RSR20-01(config-if)#ipadd192.168.1.254255.255.255.0
RSR20-01(config-if)#noshutdown
RSR20-01(config-if)#exit
RSR20-01(config)#intfa0/0
RSR20-01(config-if)#ipadd192.168.2.1255.255.255.252
RSR20-01(config-if)#noshutdown
RSR20-01(config-if)#end
RSR20-01#
RSR20-02>en14
Password:
RSR20-02#conft
Enterconfigurationcommands,oneperline.EndwithCNTL/Z.
RSR20-02(config)#
RSR20-02(config)#intfa0/0
RSR20-02(config-if)#ipadd192.168.2.2255.255.255.252
RSR20-02(config-if)#nosh
RSR20-02(config-if)#noshutdown
RSR20-02(config-if)#exit
RSR20-02(config)#intfa0/1
RSR20-02(config-if)#ipadd192.168.3.254255.255.255.0
RSR20-02(config-if)#noshutdown
RSR20-02(config-if)#end
RSR20-02#
路由器RIP路由协议配置清单
RSR20-01#conft
Enterconfigurationcommands,oneperline.EndwithCNTL/Z.
RSR20-01(config)#routerrip
RSR20-01(config-router)#network192.168.1.0
RSR20-01(config-router)#network192.168.2.0
RSR20-01(config-router)#end
RSR20-01#
RSR20-02#conft
Enterconfigurationcommands,oneperline.EndwithCNTL/Z.
RSR20-02(config)#routerrip
RSR20-02(config-router)#network192.168.2.0
RSR20-02(config-router)#network192.168.3.0
RSR20-02(config-router)#end
RSR20-02#
路由器IPSec配置清单
RSR20-01#conft
Enterconfigurationcommands,oneperline.EndwithCNTL/Z.
RSR20-01(config)#
RSR20-01(config)#access-list100permitip192.168.1.00.0.0.255?
A.B.C.DDestinationaddress
anyAnydestinationhost
hostAsingledestinationhost
RSR20-01(config)#$00.0.0.255192.168.3.00.0.0.255
RSR20-01(config)#crypto?
dynamic-mapSpecifyadynamiccryptomaptemplate
ipsecConfigureIPSECpolicy
isakmpConfigureISAKMPpolicy
keyLongtermkeyoperations
mapEnteracryptomap
pkiPublicKeycomponents
softwareUsesoftwareengineforIPSecprocessing
RSR20-01(config)#cryptoisakmp?
enableEnableISAKMP
keepaliveSetakeepaliveintervalforusewithipsecpeers
keySetpre-sharedkeyforremotepeer
mode-detectSetmode-detecttoacceptmainmodeoraggressivenegetiate
policySetpolicyforanISAKMPprotectionsuite
RSR20-01(config)#cryptoisakmppolicy?
<1-10000>Priorityofprotectionsuite
RSR20-01(config)#cryptoisakmppolicy1
RSR20-01(isakmp-policy)#authentication?
pre-sharePre-SharedKey
rsa-sigRsa-Sig
RSR20-01(isakmp-policy)#authenticationpre-share
RSR20-01(isakmp-policy)#encryption?
3desThreekeytripleDES.
aes-128AES-AdvancedEncryptionStandard(128bitkeys).
aes-192AES-AdvancedEncryptionStandard(192bitkeys).
aes-256AES-AdvancedEncryptionStandard(256bitkeys).
desDES-DataEncryptionStandard(56bitkeys).
RSR20-01(isakmp-policy)#encryption3des
RSR20-01(isakmp-policy)#hash?
md5MessageDigest5
shaSecureHashStandard
RSR20-01(isakmp-policy)#hashsha
RSR20-01(isakmp-policy)#group?
<1-2>Groupdescriptionnumber
RSR20-01(isakmp-policy)#group2
RSR20-01(isakmp-policy)#exit
RSR20-01(config)#cryptoisakmpkey?
0SpecifiesanUNENCRYPTEDpasswordwillfollow
7SpecifiesaHIDDENpasswordwillfollow
RSR20-01(config)#cryptoisakmpkey0?
WORDPre-sharedkey
RSR20-01(config)#cryptoisakmpkey0ruijie?
addressDefinesharedkeywithIPaddress
hostnameDefinesharedkeywithhostname
RSR20-01(config)#cryptoisakmpkey0ruijieaddress?
A.B.C.DPeerIPaddress
RSR20-01(config)#cryptoisakmpkey0ruijieaddress192.168.2.2
RSR20-01(config)#crypto?
dynamic-mapSpecifyadynamiccryptomaptemplate
ipsecConfigureIPSECpolicy
isakmpConfigureISAKMPpolicy
keyLongtermkeyoperations
mapEnteracryptomap
pkiPublicKeycomponents
softwareUsesoftwareengineforIPSecprocessing
RSR20-01(config)#cryptoipsec?
df-bitDf-bitsetting
security-associationSecurityassociationparameters
transform-setDefinetransformandsettings
RSR20-01(config)#cryptoipsectransform-set?
WORDTransformsettag
RSR20-01(config)#cryptoipsectransform-setruijie?
ah-md5-hmacAH-HMAC-MD5transform
ah-sha-hmacAH-HMAC-SHAtransform
esp-3desESPtransformusing3DES(EDE)cipher(168bits)
esp-aes-128ESPtransformusingAES(CBC)cipher(128bits)
esp-aes-192ESPtransformusingAES(CBC)cipher(192bits)
esp-aes-256ESPtransformusingAES(CBC)cipher(256bits)
esp-desESPtransformusingDEScipher(56bits)
esp-md5-hmacESPtransformusingHMAC-MD5auth
esp-nullESPtransformw/ocipher
esp-sha-hmacESPtransformusingHMAC-SHAauth
RSR20-01(config)#cryptoipsectransform-setruijieesp-3des?
ah-md5-hmacAH-HMAC-MD5transform
ah-sha-hmacAH-HMAC-SHAtransform
esp-md5-hmacESPtransformusingHMAC-MD5auth
esp-sha-hmacESPtransformusingHMAC-SHAauth
RSR20-01(config)#cryptoipsectransform-setruijieesp-3desesp-sha-hmac
RSR20-01(cfg-crypto-trans)#exit
RSR20-01(config)#cryptomap?
WORDCryptomaptag
RSR20-01(config)#cryptomapruijie?
<1-65535>Sequencetoinsertintocryptomapentry
local-addressInterfacetouseforlocaladdressforthiscryptomap
RSR20-01(config)#cryptomapruijie1?
ipsec-isakmpIPSECISAKMP
ipsec-manualIPSECmanualkeying
RSR20-01(config)#cryptomapruijie1ipsec-?
ipsec-isakmpipsec-manual
RSR20-01(config)#cryptomapruijie1ipsec-isakmp?
dynamicEnabledynamiccryptomapsupport
RSR20-01(config)#cryptomapruijie1ipsec-isakmp
RSR20-01(config-crypto-map)#set?
exchange-modeSetexchangemodeusingthisitem
peerAllowedEncryption/Decryptionpeer
security-associationSecurityassociationparameters
transform-setSpecifylistoftransformsetsinpriorityorder
RSR20-01(config-crypto-map)#setpeer?
WORDIPaddress(A.B.C.D)/Hostnameofpeer
RSR20-01(config-crypto-map)#setpeer192.168.2.2
RSR20-01(config-crypto-map)#settransform-set?
WORDProposaltag
RSR20-01(config-crypto-map)#settransform-setruijie
RSR20-01(config-crypto-map)#match?
addressMatchaddressofpacketstoencrypt
RSR20-01(config-crypto-map)#matchaddress?
<100-199>IPaccess-listnumber
RSR20-01(config-crypto-map)#matchaddress100
RSR20-01(config-crypto-map)#exit
RSR20-01(config)#intfa0/0
RSR20-01(config-if)#crypto?
mapApplycryptotointerface
RSR20-01(config-if)#cryptomap?
WORDCryptomapname
RSR20-01(config-if)#cryptomapruijie
RSR20-01(config-if)#end
RSR20-01#
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- 实验 IPSec 综合
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。


 《雷雨》中的蘩漪人物形象分析 1.docx
《雷雨》中的蘩漪人物形象分析 1.docx
